March 31, 2026
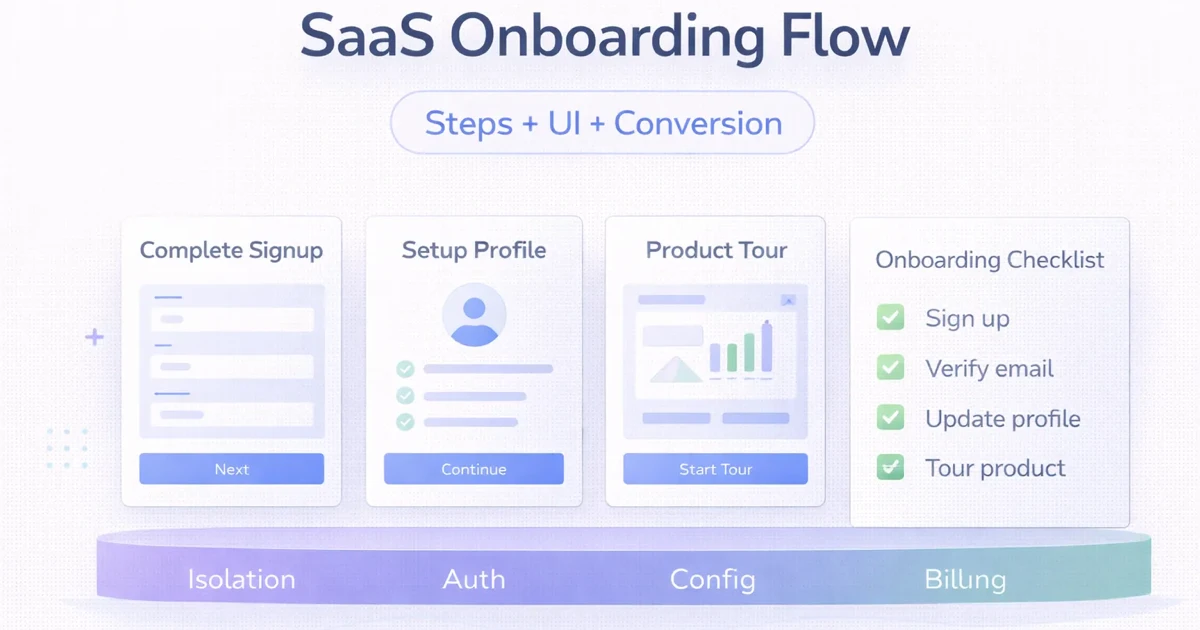
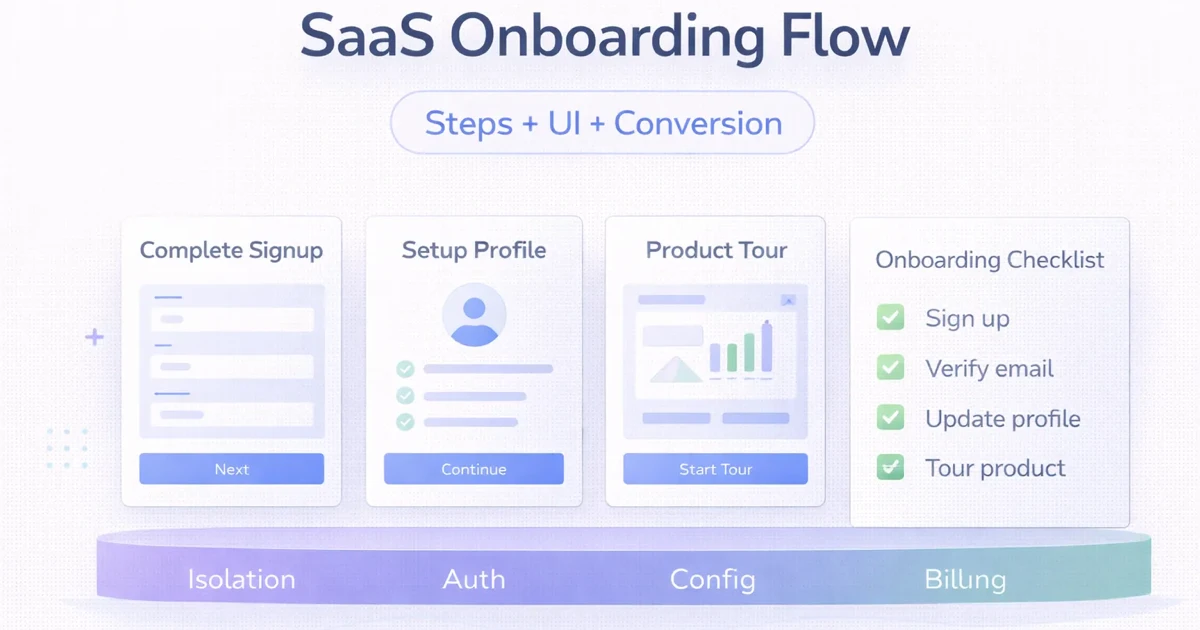
SaaS Onboarding Flow: Steps + UI + Conversion
SaaS onboarding flow guide covering steps, UI patterns, activation logic, and how to improve conversion without overwhelming new users.
Read articleMarch 31, 2026
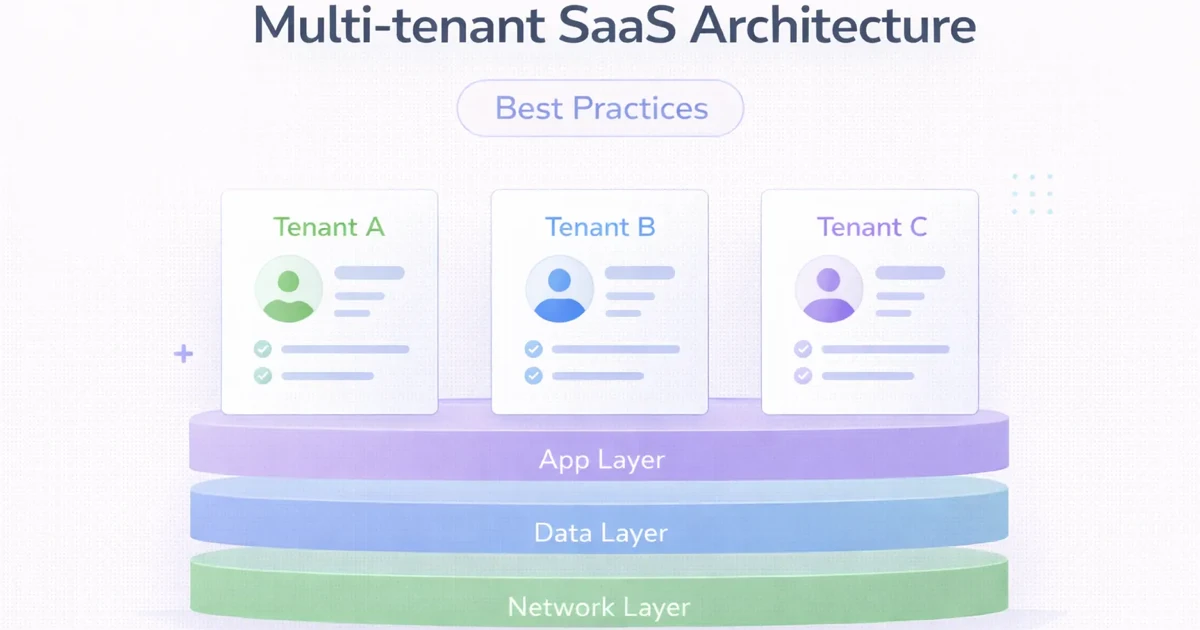
Multi-tenant SaaS architecture best practices for 2026: tenancy models, isolation, billing, observability, and what to decide early.
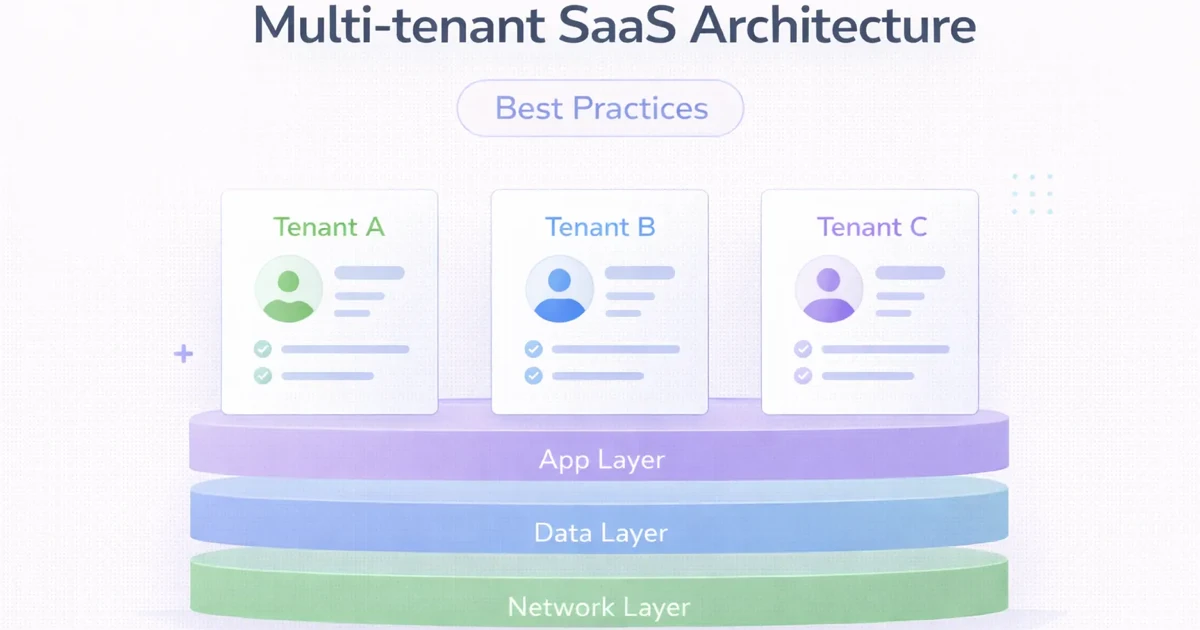
Many SaaS products start as a single-customer application and only later try to "make it multi-tenant." That usually creates messy access control, weak data isolation, brittle configuration handling, and painful billing logic. Multi-tenancy should be designed intentionally, even if the first version is simple.
The goal is not only to put multiple customers inside one application. The goal is to do it safely, efficiently, and in a way that still supports growth. A weak tenancy model can slow the entire product team later.
This guide explains the main multi-tenant architecture choices, what to decide early, and what best practices matter most in 2026.
For most early B2B SaaS products, the best starting point is:
The most important rule is simple: tenant identity should be a core system concept, not a later patch.
Best for:
Risk:
Access control mistakes become dangerous if tenant scoping is weak.
Best for:
Risk:
Operational complexity rises quickly.
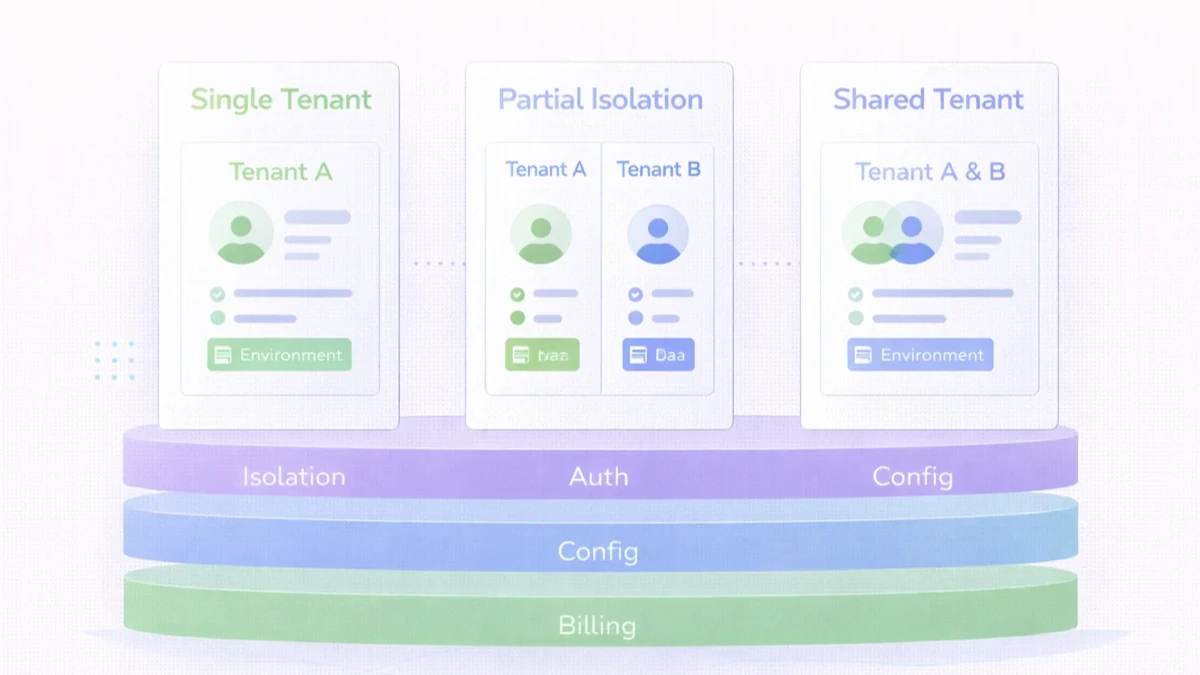
Some SaaS teams keep standard customers in a shared model and larger enterprise tenants in a more isolated setup.
That can be practical, but only if the product team manages the added complexity deliberately.
Related reading:
Every important record should know which tenant it belongs to.
User roles, admin privileges, and cross-tenant restrictions must be designed early.
Some tenants need different feature flags, branding, limits, or workflows. Decide where that lives.
Subscription state should influence tenant-level capabilities cleanly.
Do not rely on UI assumptions. Tenant boundaries should exist in backend logic and data queries.
Login tells you who the user is. Authorization tells you what they can do inside a tenant.
Logs, metrics, and error traces should help you identify tenant-specific issues quickly.
Even if you start shared, plan for future isolation or data movement paths.
Too many per-customer custom branches destroy product maintainability.
Next.js or React frontend with tenant-aware routing where neededNode.js or equivalent backend for authorization, tenancy, and API logicPostgreSQL with disciplined tenant scopingThe biggest cost drivers are:
If your product is becoming multi-customer, do not keep adding tenant logic ad hoc. The right time to define tenancy boundaries is before data and permission mistakes become expensive.
It is an architecture where one SaaS platform serves multiple customers while keeping their data and access separated.
Not necessarily. It can work very well if tenant scoping and authorization are implemented carefully.
Usually when isolation, compliance, or enterprise requirements are stronger.
Treating tenant identity as an afterthought.
In most B2B SaaS products, tenant-level billing is more practical.
Yes, but the migration is easier if you design for it from the start.
Often yes, especially when plans or enterprise requirements vary.
Both matter, but a weak tenant-aware data model causes deeper long-term pain.
If you want a SaaS architecture that supports more customers, safer isolation, and clearer product control, the next step is to define tenancy, authorization, and configuration rules before scaling feature work.
Related Articles
March 31, 2026
SaaS onboarding flow guide covering steps, UI patterns, activation logic, and how to improve conversion without overwhelming new users.
Read article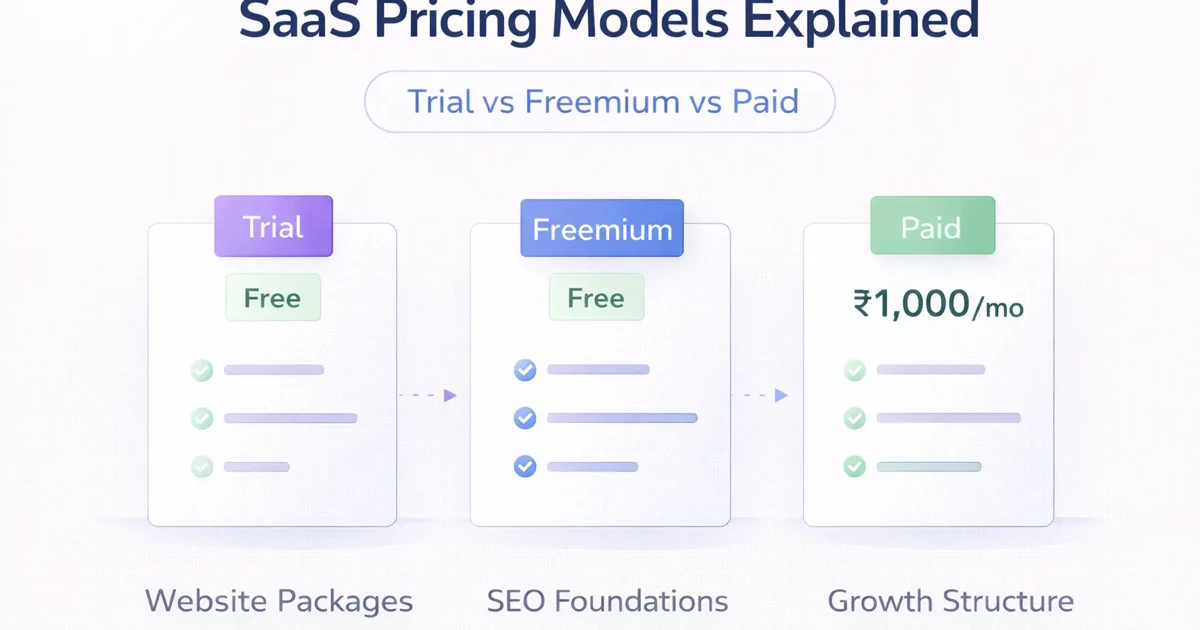
March 31, 2026
SaaS pricing models explained for India: trial vs freemium vs paid, plus flat-rate, seat-based, and usage pricing advice for founders.
Read article
March 25, 2026
Cloud-based software for SMEs in 2026: why it is better for access, updates, reporting, integrations, and growth than older offline business software setups.
Read article